The rise of neobanks has been one of the most defining shifts in modern financial services. Sleek mobile interfaces, rapid onboarding, and customer-centric design have helped digital-first banks attract millions of users globally. Yet behind the seamless user experience lies a complex - and often misunderstood - security landscape. As neobanks scale through partnerships rather than traditional infrastructure, a critical question emerges: who actually owns payment security?
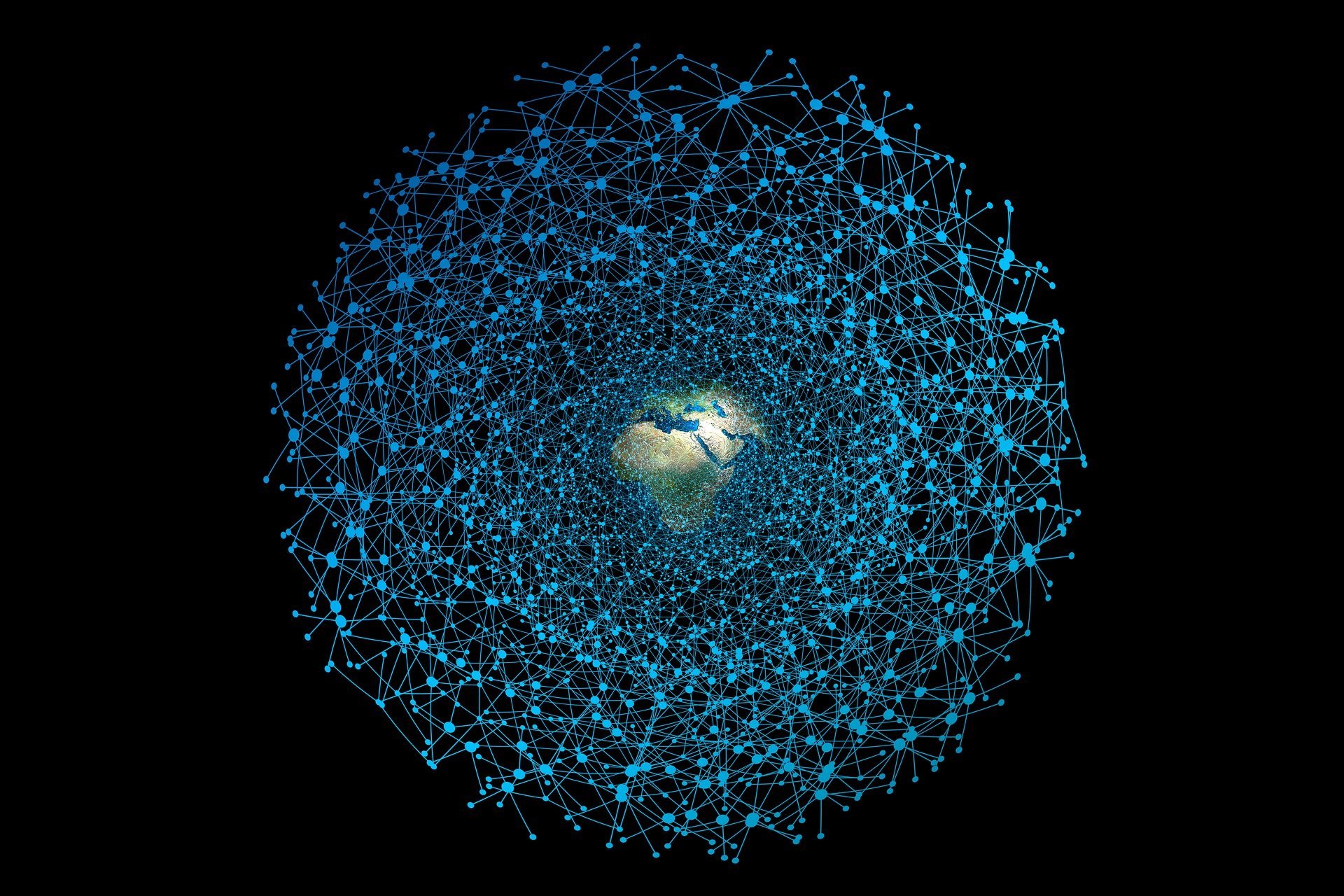
Neobanks didn’t grow by building banks from the ground up. They leveraged a network of partners, including Banking-as-a-Service (BaaS) providers, payment processors, sponsor banks, and card networks. This approach enabled rapid expansion across regions like Europe, the United States, and Asia. However, this speed came with trade-offs. Unlike traditional banks, neobanks rarely control the full technology stack. Instead, they orchestrate a network of third-party providers, each handling a piece of the transaction lifecycle.
To the end user, a neobank appears to be a single, unified entity. In reality, the architecture is anything but simple. A typical card transaction may pass through the neobank’s app, a BaaS platform, a sponsor bank, a payment processor, and the card networks. Each entity may store, process, or transmit cardholder data at different points. This creates a critical ambiguity: if multiple parties touch sensitive data, who is ultimately responsible for securing it?
The Payment Card Industry Data Security Standard (PCI DSS) is designed to protect cardholder data wherever it is handled. In traditional banking, scoping PCI responsibilities is relatively straightforward. In neobank ecosystems, it becomes significantly more complex. Distributed data flows, tokenization layers, cloud-native infrastructure, and third-party dependencies all increase the difficulty of maintaining robust security and clear accountability. While neobanks often rely on partners to manage PCI compliance, reliance does not transfer responsibility. Ultimately, the neobank retains accountability for the security of its customer’s data.
Neobanks operate under a model similar to cloud computing: shared responsibility. Unlike cloud providers, however, the fintech ecosystem often lacks clear definitions for who owns each security responsibility. While processors may be PCI compliant and sponsor banks regulated, gaps can still emerge in API security, data handling, logging, and incident response. This leads to a dangerous assumption: that someone else is handling the risk. In reality, risk is shared, but accountability is often blurred.
The way neobanks manage security and compliance varies by region. In Europe, regulatory frameworks and open banking initiatives create structured environments but also increase API exposure. In the United States, heavy reliance on sponsor banks and BaaS providers introduces layered dependencies and regulatory complexity. In Asia, highly integrated ecosystems and “super apps” consolidate services, which can reduce fragmentation but increase concentration risk. These differences directly impact how PCI DSS is interpreted, implemented, and enforced.
While neobanks offer convenience and innovation, their architecture introduces distinct risks. Over-reliance on a small number of providers, expanded attack surfaces through APIs, compliance blind spots, and potential exposure to fraud all make security a critical concern. Perhaps the biggest risk is organizational: a lack of clear ownership over security responsibilities can leave users exposed, even when technical controls exist.
As the neobank sector matures, scrutiny on security and compliance will increase. We can expect more regulatory focus on third-party risk, greater demand for transparency in security ownership, and a push toward stronger internal security capabilities. Some neobanks may move toward obtaining full banking licenses, while others will need to strengthen governance across their partner ecosystems.
Neobanks have redefined how financial services are delivered - but not how risk is eliminated. In a fragmented architecture, security cannot be assumed, outsourced, or abstracted away. It must be clearly owned. Because in the end, when it comes to protecting cardholder data, shared responsibility without clear accountability is a risk in itself.
If you would like to get in touch with us to discuss how we can support your cybersecurity needs - please reach out to us: hello@onecybervalley.com
By 1 Cyber Valley | April 13th, 2026 | Suhema Sashtikar


.png)