The rapid adoption of electric vehicles (EVs) has led to an equally rapid expansion of public and private vehicle-charging infrastructure. Charging stations are now commonly found in parking lots, shopping malls, offices, hotels, and other public spaces. Many of these charging stations support digital payments, mobile applications, cloud connectivity, and remote management systems.
While this ecosystem provides convenience for EV users, it also introduces a new attack surface for cybercriminals. From a security and compliance perspective, this raises an important question: Are EV chargers a hacker’s dream, or are they being built with sufficient security safeguards? And more specifically, do they fall within the scope of PCI DSS when payment card data is involved?
The Growing Attack Surface of EV Charging Infrastructure
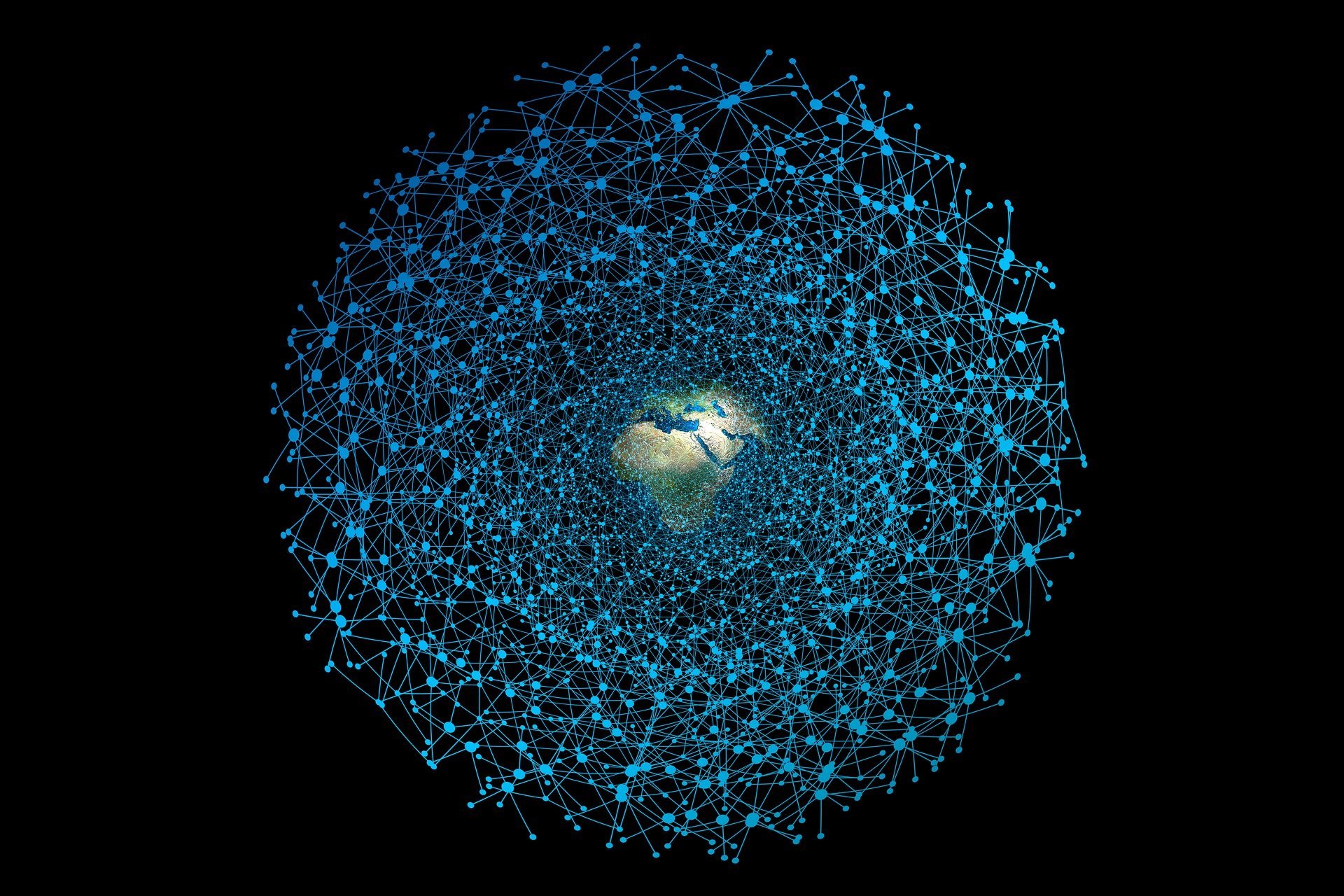
Modern EV chargers are no longer just electrical devices. They are connected systems that interact with cloud platforms, mobile applications, payment systems, and network infrastructure. A typical EV charging ecosystem includes charging hardware, backend management platforms, mobile applications, and network connectivity such as Wi-Fi or cellular networks.
Because of this connectivity, EV chargers function similarly to IoT devices with payment capabilities, which increases the potential attack surface. Insecure firmware, weak authentication mechanisms, or unencrypted communications could allow attackers to manipulate charging sessions, intercept communications, or even gain access to backend systems.
Why Hackers May Target EV Chargers
EV charging infrastructure can be attractive to attackers for several reasons. Chargers that accept card payments may process sensitive financial data, making them potential targets for payment fraud or data theft.
In addition, charging networks are often large and distributed. This means a single vulnerability in a centralized management platform could affect multiple chargers simultaneously, similar to many IoT ecosystems. Some chargers may also suffer from weak security controls such as default credentials, outdated firmware, or poor patch management, making them easier entry points for attackers.
Are EV Chargers in Scope for PCI DSS?
Whether EV chargers fall within the scope of PCI DSS depends entirely on how payment transactions are handled. Let’s look at a few common scenarios.
Scenario 1: Charger Accepts Card Payments Directly
If the charging station includes a card reader and processes card data, it functions similarly to a point-of-sale (POS) terminal.
In this case, the charger itself becomes part of the Cardholder Data Environment (CDE) and must comply with PCI DSS requirements. Secure payment processing and strong encryption mechanisms must be implemented, and the hardware may need to be PCI PTS-approved if it captures cardholder data.
Scenario 2: Payment Handled Through a Mobile Application
Some charging networks require users to initiate charging through a mobile application, where payment details are stored and processed through a backend payment gateway.
In this scenario, the charger itself may not directly handle card data. Instead, the mobile application and backend payment systems fall within PCI DSS scope. The charger may remain out of scope, provided it never processes, stores, or transmits cardholder data.
Scenario 3: QR Code or Redirected Payments
Some EV chargers display a QR code that redirects users to a payment page hosted by a third-party payment processor.
In this case, the charger does not process cardholder data, and the payment occurs entirely on the secure platform of the third-party payment provider. As a result, the charger may remain out of PCI DSS scope. However, security controls are still recommended to protect the broader infrastructure.
Are EV Chargers a Hacker’s Dream?
EV chargers have the potential to become high-value targets due to their connectivity, widespread deployment, and financial integration. If the EV charging ecosystem is poorly designed, it could become a hacker’s dream, enabling attacks ranging from payment fraud to large-scale infrastructure disruption.
However, when built with secure architecture, strong network segmentation, encrypted communications, and compliant payment processing mechanisms, EV charging systems can be effectively safeguarded while supporting the continued growth of EV adoption.
Conclusion
EV charging infrastructure is a rapidly growing part of the connected technology landscape, merging transportation systems with financial and IoT ecosystems.
From a PCI DSS perspective, EV chargers are only in scope when they directly process, store, or transmit cardholder data. If payments are handled securely through external systems such as mobile applications or third-party payment gateways, the chargers themselves may remain out of scope.
However, organizations should not assume that being out of PCI scope means being risk-free. Strong cybersecurity practices remain essential to protect users, financial transactions, and the broader charging network. As EV adoption continues to accelerate globally, securing EV charging infrastructure will become an increasingly important focus for both the cybersecurity and compliance industries.
If you would like to get in touch with us to discuss how we can support your cybersecurity needs - please reach out to us: hello@onecybervalley.com
By 1 Cyber Valley | March 9th, 2026 | Harshita Yadav


.png)





.jpg?width=352&name=shutterstock_2296846207%20(1).jpg)

